Follow us on Facebook
Breaking updates in your feed — tap to open
The smartphone security environment is developing at a high rate and the emerging threats will come in more advanced forms by the year 2026. With the rise in cases of spy incorporation, and an increasing number of individuals becoming conscious of their privacy matters when using not only flagship smartphones but also low-end smartphones, knowledge of how to secure your mobile phone or device has never been more important than today. This guide has practical steps that will be applicable in either situation where a person is using an iPhone with the most recent features of the iOS update or an android phone with Samsung, Google Pixel or OnePlus. Security has its principles that are beyond the operating systems and costs making it a need that is universal to be on the alert.

- Getting to know the Modern Mobile Vulnerabilities
- The most important part of smartphone protection is the secure data storage
- The use of app permissions is something that should be regularly watched
- Best Practices in Biometric Security
- The identification of phishing attacks on mobile users has proved to be more difficult
- The digital security is supplemented by physical protection of devices
- Making Your Digital Ecosystem More Secure
- The most simple type of defense against new threats is regular updates
- Moving forward to 2026, artificial intelligence is therefore likely to change smartphone security
- The current proactive security will set habits that guard against the long run threats that are not yet known tomorrow
Getting to know the Modern Mobile Vulnerabilities
Smartphone protection starts with the awareness that threats have changed to go further than conventional viruses. The current attackers also focus on particular weaknesses of the app permissions, data storage processes, and even biometric security protocols. The use of 5G networks and the growth of cloud storage has increased the threat of attacks many folds. What most users do not know is that the settings of their devices to optimize their performance and battery life can affect their security, and the add-ons available such as charging their devices rapidly and wireless charging stations can pose further issues in case of access in compromised cases.
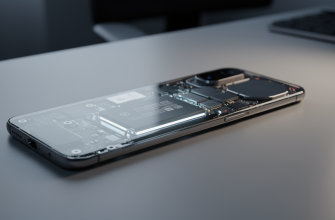
The most important part of smartphone protection is the secure data storage
Encryption must be the backbone to secure your local storage or it must be your first line of defense when using cloud services. In case of devices that have a large storage space, you can split sensitive information into a different part as compared to other daily applications and entertainment. Routine backups are also very necessary although make certain that the backups themselves are secured by high-authentication. USB-C has been adopted by majority of the new devices and this has made connections uniform, however this also comes along with the knowledge of how to maintain good cable security when exchanging information.
The use of app permissions is something that should be regularly watched
Only grant app reviews to apps that process sensitive data such as financial data or personal messaging. Especially beware of gaming applications that need un-needed permissions, and productivity tools that may be looking further than its purpose. Note that despite the well-foundedness of specific apps, they may fall under the classification of vulnerabilities as long as their authorization is too expansive or when they fall victim to security breaches.

Best Practices in Biometric Security
Most smartphones, including foldable phone models and other conventional ones, support biometric authentication systems such as scanners that can retrieve fingerprints and facial images. Although such systems are convenient, they should be correctly established and reviewed periodically. Always remember to get several angles or fingerprints on your prime biometric process and have a strong password in reserve. In devices that have a developed camera system with the possibility of performing much of the night mode photo shooting as well as portrait mode, it is necessary to know that the facial recognition systems are built on the same sensors, and therefore, the security of this feature is directly linked to the overall camera quality on the device.
The identification of phishing attacks on mobile users has proved to be more difficult
In contrast to regular email phishing, the mobile attack can be in form of messages, social media, or even hacked legitimate programs. Be especially aware of those messages that ask to take immediate action or promise too-good-to-be-true offers on accessories or devices. be cautious of such links talking of having special access to rumors or leakage about future devices, these links usually provide access points to malware.
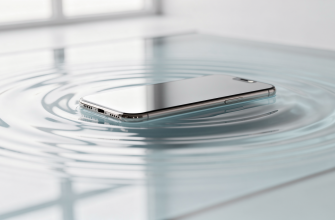
The digital security is supplemented by physical protection of devices
Waterproof ratings and durability test will bring information related to the stand of a device; however, physical security covers the aspect of preventing unauthorized access by lost or stolen devices. See the tracking services on sites or apps such as Google Find My device or Apple Find My system, but be aware of both of them. In case of the devices that have OLED screens and high refreshing rate advantages, it is better to consider the use of screen protectors in conjunction with biometric sensors without compromising essential security measures.

Making Your Digital Ecosystem More Secure
Smartphone security is not an isolated item on its own, but a component of your wider digital ecosystem that includes wearables such as Apple Watch or Fitbit devices, productivity tablet devices, and smart home systems. Secure practice should be applied throughout all the linked devices especially in cases where they exchange data or authentication processes. Users with a variety of devices will find that their security measures are always consistent across all the devices to eliminate the chances of one device being compromised to undermine those devices. Particularly, this is relevant to individuals whose smartphones double as devices on which wearable fitness applications or smart home concepts can be accessed.
The most simple type of defense against new threats is regular updates
Regardless of whether you are under Android and its frequent updates functionality or under iOS and its routine improvements, updates will solve known weaknesses. To those who are worried about performance implications, keep in mind that security patches do not usually affect battery life and gaming phone performance much, and must offer the necessary protection. Manufacturers are putting more consideration on security in their period of updating especially on flagship devices which will have long-term support.
Moving forward to 2026, artificial intelligence is therefore likely to change smartphone security
In the future, users must be ready to face even more customized phishing or even even more advanced malware which is able to learn personal usage behaviors. The growth of foldable phones and new form factors will bring forth new security considerations, especially concerning the display durability and hinge mechanisms which may include more sensors. Likewise, developing technologies in audio devices like AirPods, Galaxy Buds, and other Bluetooth earbuds will provide new avenues of interception where data can be captured, and current security models do not sufficiently deal with it.
The current proactive security will set habits that guard against the long run threats that are not yet known tomorrow
It starts by conducting a detailed audit of your existing security habits, starting with permission of apps up to biometrics settings. Put into thinking how your usage patterns, such as mobile photography, gaming, and student productivity, have certain weaknesses that demand unique solutions. It is essential to keep in mind that security does not entail removing any risk; it is rather choosing defense upon defense to secure your most valuable information and not altering the functionality that makes contemporary smartphones the tools you could not do without. Having reached 2026, this middle ground will be more beneficial than any of the one-dimensional security features or settings.