Follow us on Facebook
Breaking updates in your feed — tap to open
- Getting to Know the Low-Power Mode
- The most highly used use of this technology is Apple Find My network
- Emergency Functions and Transmission of Data
- The primary considerations in this design are privacy considerations
- When examining the impact of the battery, there is engineering that would be studied
- This system as far as security is concerned is supposed to be a fortress
- To the user, who appreciates absolute control, the existing implementation is not that appealing
- The consequences continue to other discussions on device ownership and digital autonomy
- Finally, the capability of the current iphone to stay partially on and off is a complex mixture of both hardware and software aimed at keeping the device safe and comfortable to the user
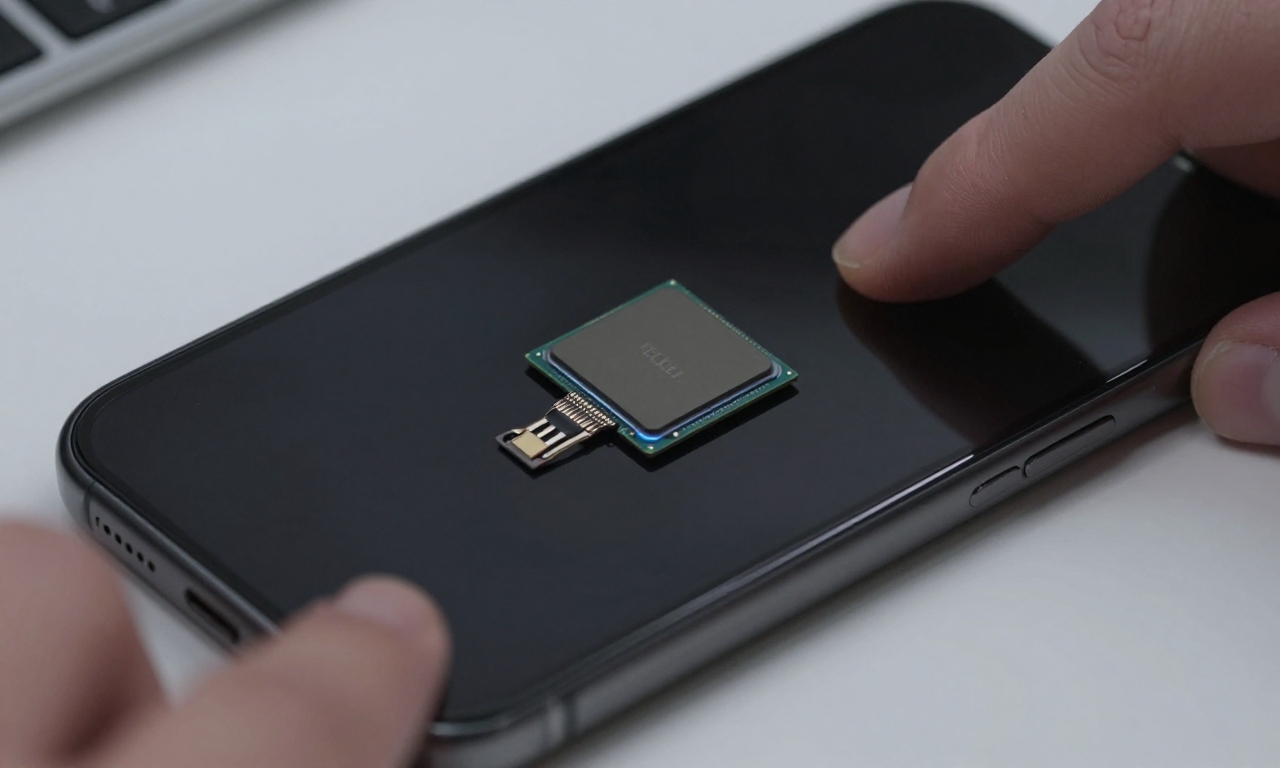
Getting to Know the Low-Power Mode
This consistent operation is made achievable via a keyed ultra-low-power chip that is not shut off. Producing a shutdown with the software simply turns out the main processor and display but this secondary chip still consumes a small portion of battery. Its main function is to eavesdrop in order to pick out certain signals. This design enables the device to do basic routines without complete booting up of the main system which would take a toll on the available battery life.
The most highly used use of this technology is Apple Find My network
In case your iPhone gets lost or stolen and somebody has shut down the phone, it can still transmit a secure Bluetooth signal. This signal is detectable by other Apple products that will transmit the location in an anonymized and encrypted fashion to iCloud. This forms an expansive and crowdsourced tracking network. To the user, it translates to an extremely greater likelihood of having a lost device recovered, where the purchasing guide into the iPhone decision is taken by ticking hardware or an ecosystem of protection.

Emergency Functions and Transmission of Data
In addition to being able to recover the device, this low-power state is able to enable life or death emergency functions. As an example, making of emergency SOS calls through satellite on models that are supported is based on this underlying architecture. The nature of data being transmitted in this state is highly restricted and encrypted. As a rule, it contains only that minimum of identifiers required by Find My location pings or emergency handshakes. No personal files, messages or the history of browsing is transmitted in this dormant state.
The primary considerations in this design are privacy considerations
Apple notes that all the communications are encrypted and anonymized end-to-end. When a different device picks up the Bluetooth signal of your iPhone, it is not aware of who is device it belongs to, or whatever personal information; it just forwards encrypted positioning information. But to the users who have very high privacy requirements this always-on facility is questionable. The need to have a full-fledged, verifiable shutdown in which there are no active parts is antagonistic to the convenience and contractual safety these attributes offer.

When examining the impact of the battery, there is engineering that would be studied
The chip is dedicated, and requires a really small amount of power which, in this state, is supposed to run a fully charged battery in several weeks or even months. This is a trade off that Apple has estimated that most users will pay to secure an advantage. This drain is insignificant at the everyday usage (on the display, the cellular radio, and the apps) to optimize the battery life. But, in the event of leaving a phone unused and storing it over a long period, it is a consideration.
This system as far as security is concerned is supposed to be a fortress
The very small chip is powered on its own secure enclave, not part of the main iOS. It can never be reprogrammed and can only be accessed through physical hardware-level attacks that will be noticeable. This renders the use of this continuous condition very hard to allow malevolent individuals to use it to spy on people. The security model presupposes a physical device trusted and is aimed at the defense against intercepting information towards external information grabbers and not against the owner of the device.
To the user, who appreciates absolute control, the existing implementation is not that appealing
This low-power mode has no easy software switch to switch it off completely. To attain a complete zero communication and this would be the real shutdown where the communication reduces to zero, one would have to allow the battery to run out to zero. In this analysis we can see a change of the way we think about our devices they are not as basic as a tool we often turn on and turn off but rather a node within a network even when we are not actively using them.
The consequences continue to other discussions on device ownership and digital autonomy
Although the advantages of recovery and safety are obvious and are consistent with the current tendencies in the reviews of flagship smartphones that said nothing but glorified built-in security, something non-aqueous is lost. This will mirror an ever-greater trend in the industry where convenience and connectedness is taken into account more than absolute user control at the hardware level.

Finally, the capability of the current iphone to stay partially on and off is a complex mixture of both hardware and software aimed at keeping the device safe and comfortable to the user
It makes it possible to have powerful features such as Find My network, emergency services with little battery usage and high privacy. But it is also a radical shift in the relationship of the device with the user, which no longer considers a complete digital disconnect in the network in favor of built-in security and locating a lost phone.








